You might have heard about “the impossible triangle” which has triggerred heated discussion in cryptocurrency communities.
We will discuss whether it is a true concept or a pseudo one, because only when we can distinguish the authenticity and no longer waste time on the pseudo one, it is possible to explore the issues worthy the efforts in the blockchain.
This article is composed of three parts: the history of impossible triangle; the questioning of impossible triangle; the distributed system CAP theorem is the real impossible triangle.
Misunderstood History of Impossible Triangle Evolution
The impossible triangle of blockchain refers to a blockchain system which cannot satisfy three angles at the same time. It must improve the index of the other two angles at the expense of one certain angle.
Changjia Version
In China, it’s Changjia who proposed the theory of impossible triangle for the first time. In 2014, he published an article entitled Impossible Triangle: Security, Environmental Protection and Decentralization, which aroused extensive discussion.
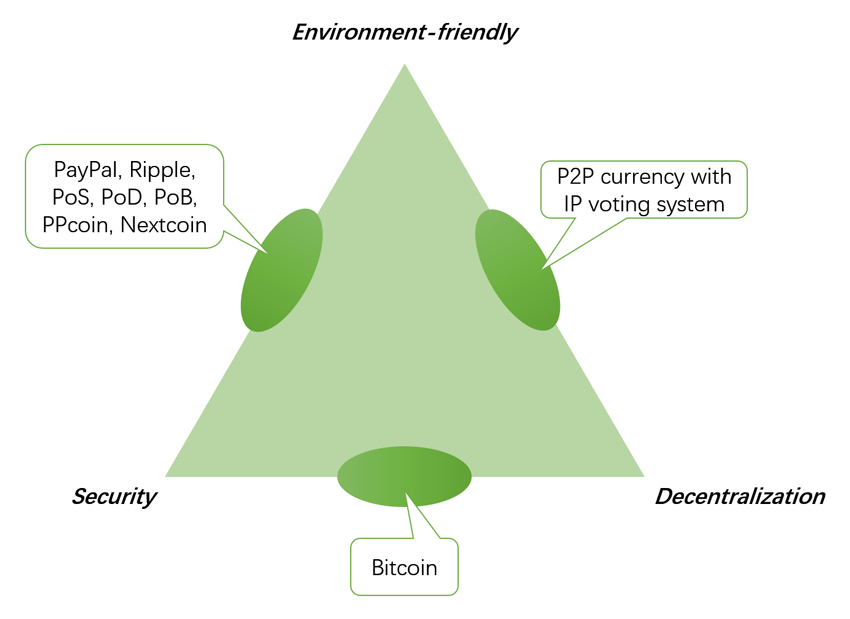
However, this article discusses the impossible triangle of cryptocurrency and concludes that “environment-friendly cryptocurrency” does not exist. It’s completely different from the applicable field of the impossible triangle we are talking about today. Changjia described the impossible triangle as follows:
Here, I propose a ternary paradox: decentralization, security and environmental protection constitute an impossible triangle.
To design an environment-friendly and secure cryptocurrency, it must be centralized, such as PPcoin, Nextcoin and Ripple. They are either centralized structures or their decentralized architecture is unsustainable. They still belong to the centralized verification mechanism like PayPal and online banking.
It must be unsafe to design a cryptocurrency which is both environment-friendly and decentralized, such as the P2P currency with IP voting system. Nakamoto ruled out such possibility at the very beginning because he thought “if the approach deciding the majority was based on the IP address with one vote for one address, those who owned the power to allocate a large number of IP addresses, such as the botnet, it was possible for them to dominate the bitcoin network.”
Designing a safe and decentralized cryptocurrency should necessarily be at the expense of energy and hash. The POW is the first solution to build a secure property certification system in a decentralized form, and it might be the only solution.
The “decentralization” and “security” proposed by Changjia is the same as the popular versions now, but the meaning they represent is quite different. What is referred to in his version is the mechanism and security of currency.
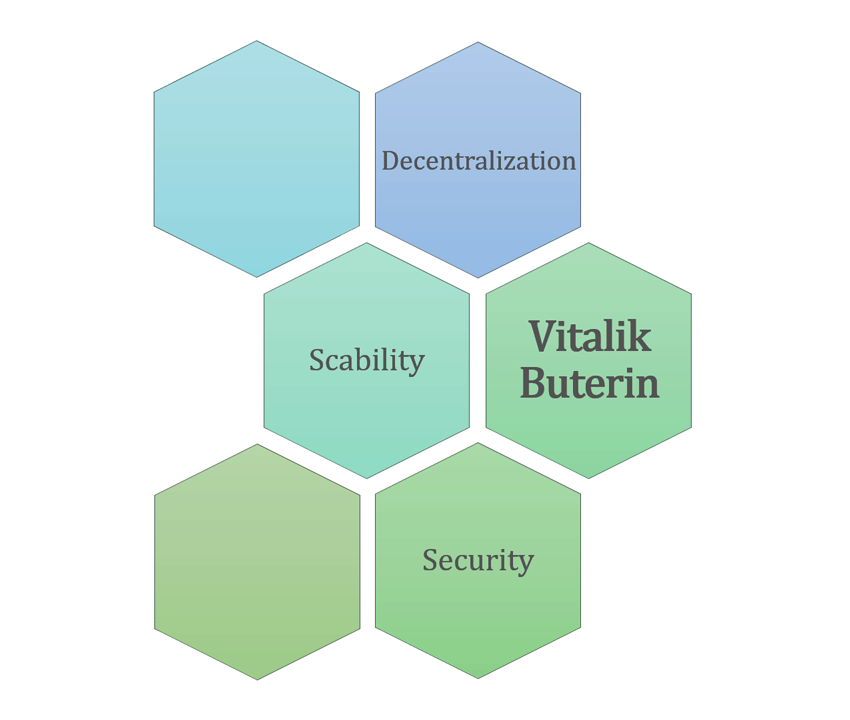
Vitalik Buterin Version
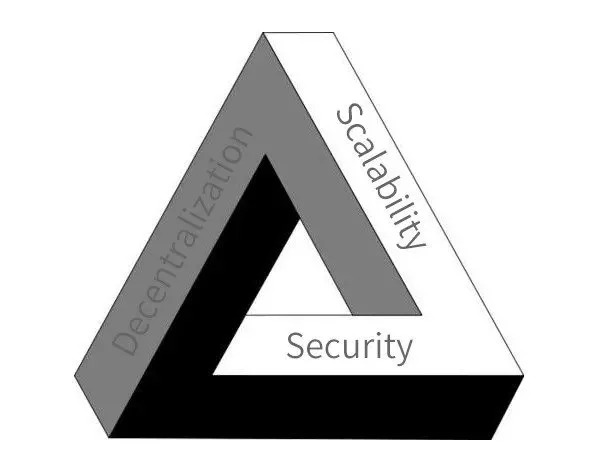
The most popular version of the impossible triangle theory is the one by “Vitalik”. What proposed is that blockchain system cannot simultaneously combine decentralization, scalability and security. The triangle is widely quoted in various presentations, reports, articles and even white papers.
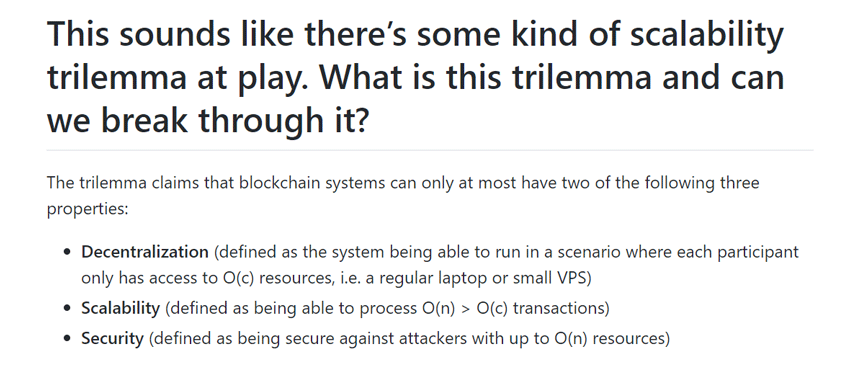
This impossible triangle originated from an article in the GitHub Ethereum catalogue entitled On sharding blockchains, in which the trilemma was initiated for the first time.
This article is a part of the Sharding FAQs series of Ethereum, which was created and maintained by a team member named James Ray. What’s the purpose of this series? It’s used to answer all the questions about sharding.
That is to say, the so-called theory initiated by Vitalik was only mentioned by the Ethereum team member in an article answering community questions. It’s not a research paper and irrelevant to Vitalik and it’s not even a thematic article. But the truth is not only limited to the aforesaid aspects.

For the sake of better illustration, some facts about the “Vitalik”-version impossible triangle are explained one by one as follows:
- The original text is “This sounds like there’s some kind of scalability trilemma at play”. Combined with the context, it’s easy to find out that the theory of impossible triangle has not been subject to any logical and systematic argument. The author only enumerated some questions and then initiated the viewpoint. Moreover, the author used the expression with uncertainty in the text, which, however, was regarded as the undoubted truth later.
- The “scalability” had been discussed in the original text and even the author called it “scalability trilemma”. That is to say, this triangle was only for “blockchain scalability”, but it’s extended to “blockchain” from Scalability Trilemma to Blockchain Trilemma.
- For the triangle: Decentralization, Scalability and Security, the author made a clear definition, such as security “being secure against attackers with up to O(n) resources”. That’s to say, the triangle mentioned by the author was under a premise but it’s extended to a more broader spectrum.

However, the biggest problem with the “Vitalik” impossible triangle is not the aforesaid facts, but the environment in which this viewpoint was initiated. It appeared in the article introducing Ethereum sharding technology.
Those who have written academic papers must know that in order to prove their researches can solve problems, the first step was usually to raise questions; to prove the effectiveness of their researches, they usually described the problem very important and difficult to be solved. The article On sharding blockchains is exactly written in the same structure.
It described the status first to raise the question of “impossible triangle”; then, it adopted various methods to analyze and pointed out that others couldn’t solve this problem; finally, it proposed his own solutions to demonstrate how the method could solve the problem perfectly.
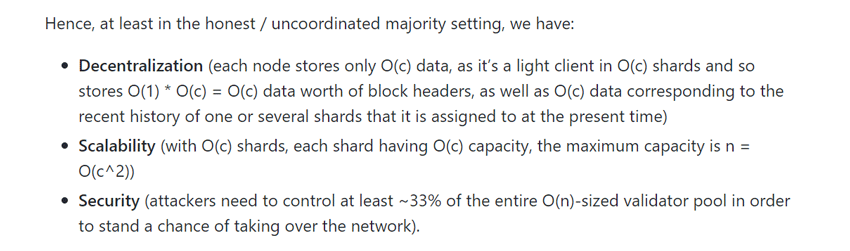
Yes, if the readers are patient enough to read the whole article on the “Vitalik” impossible triangle, they will find that Ethereum has solved this triangle problem through its sharding technology. The so-called “impossible” has been demonstrated as “possible” on the first day of its birth.
James Ray wrote this impossible triangle in his article just to demonstrate that Ethereum could achieve scalability through sharding technology. He just wanted to prove “we can break through scalability trilemma”.
About this triangle, the article has given clear and rigorous definition. However, it was later misunderstood and misinterpreted. The following picture shows the extent of solution which Ethereum can achieve.
Groundless Impossible Triangle
The impossible triangle theory has been widely recognized, partly because of the popularity of Changjia and Vitalik. But does it really stand up to scrutiny?
Why not ask following three questions first?
- What is decentralization? What is scalability? What is security? Can you answer their respective meanings exactly? If a theoretic concept cannot be accurately defined, what is the value of the theory?
- Reduce the three constituents to two, does the contradiction of “impossibility” still exist? Increase three constituents to four, and does it still exist? If so, what is the exact meaning of the “impossible triangle”?
- What’s the practical guidance of the impossible triangle on the implementation of blockchain project?
“Scalability ” has been replaced by “performance” in a few versions, but even if it hasn’t been replaced, people can still semantically use “scalability” to refer to “performance.” But the two concepts are not equivalence. Scalability is just one of the ways to improve performance. Performance is just one of the features of the implementation of scalability. The figure below is a common version of the impossible triangle.
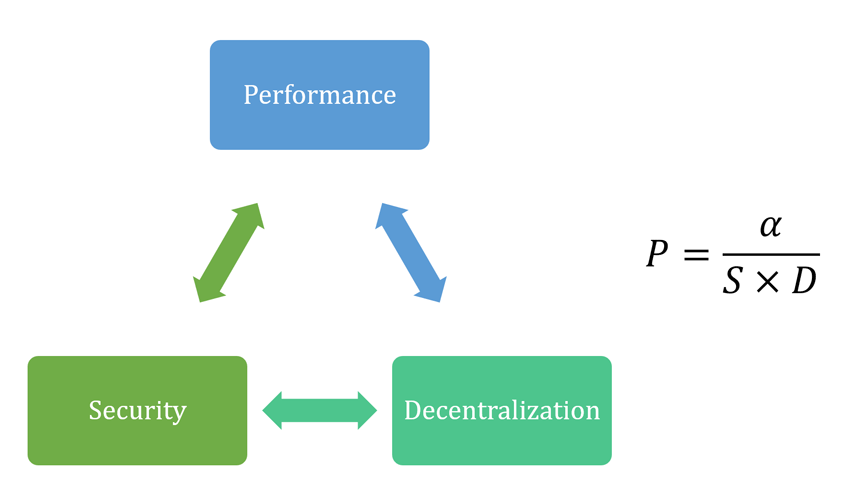
The EOS 21 nodes are often used to prove the correctness of impossible triangle. People believe that it sacrifices “decentralization” for the sake of “performance”, but what concerns us about the “decentralization”? We worry the EOS is not “safe” because of its centralization. Decentralization and security are closely relevant with each other.
The two of “decentralization” and “performance” as constituents is perhaps enough for the “impossible” theory, because that two factors can already explain the current dilemma of blockchain.
In the other aspect, can sacrificing decentralization and scalability ensure the security of blockchain system? Obviously not. Security mostly belongs to the pure technical solution, then what does the security in the impossible triangle refer to? What is the meaning of advocating limited security?
In addition to “exaggeration”, the impossible triangle cannot provide any practical guidance for the engineering implementation of blockchain project. We can’t imagine the project manager tells his team members, “To improve performance, we can compromise the security of the system.” Or “For the sake of decentralization, compromise the high performance of the system.”
This is the case. No projects would improve one of the aspects at the cost of others.
Distributed system CAP theorem is the real impossible triangle
Despite the different versions of “impossible triangle” , pehaps the original distributed system CAP theorem is actually the most precise and most relevant one in which CAP refers to consistency, availability and partition tolerance.
Eric Brewer proposed the CAP at the ACM PODC Symposium (ACM Symposium on Principles of Distributed Computing). Then, Seth Gilbert and Nancy Lynch from MIT theoretically proved the it and made it a theorem.
The CAP theorem is one of the most important principles in the field of distributed systems, which profoundly affects the development of distributed computing and system design.
The specific meanings of CAP theorem consistency, availability and partition tolerance are as follows:
- Consistency: If the system returns a successful write operation, then the subsequent read request must read the new data; if the return fails, then all read operations cannot access to the data, so the data is highly consistent to the caller.
- Availability: All read and write requests can be responded within a certain period without always waiting.
- Partition tolerance: The network in the system may suffer from partition failure, that is, communication between nodes cannot be guaranteed, but it does not affect the normal service of the system.
According to the CAP theorem, a distributed system can only implement two of aforesaid three elements at the same time.
- If the AP is satisfied at a certain moment, that is, the separated node external service without mutual communicate, it will result in inconsistency which cannot meet the condition of C;
- if the condition of CP is met, then in the case of network partition, the request can only wait to meet the condition of C, so the condition of A cannot be met;
- if the condition of CA is met, that is, the node status is consistent within a certain period, then the network partition cannot be realized, which will not meet the condition of P.
The conclusion tells cryptocurrency designers not to waste time trying to satisfy all these three factors, because it is impossible.
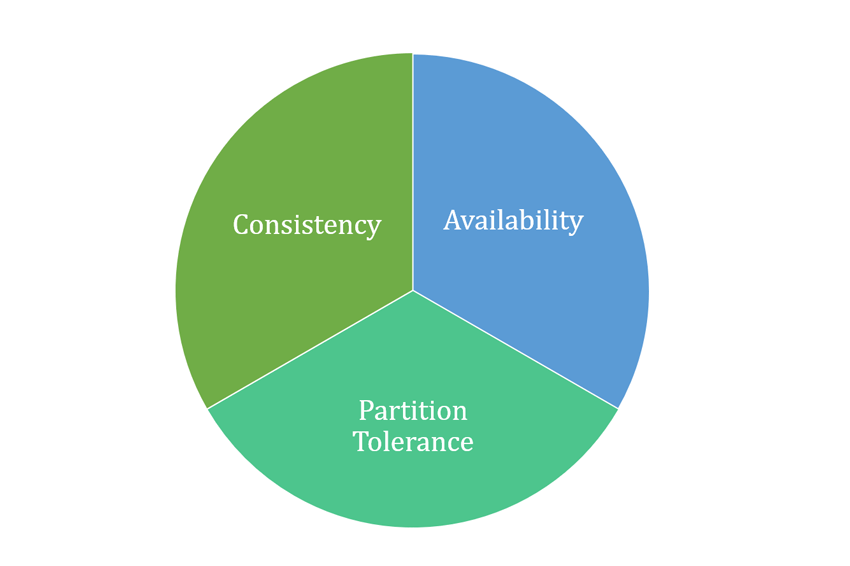
Under the premise of the impossible triangle, diversified currencies have been issued satisfying two of those three aspects of the triangle.
In the blockchain, the consistency can ensure that the data read by each node in each chain is always the same. The availability is to ensure that each node in each chain can realize transactions without completed synchronization, and because the nodes are distributed and the partition tolerance must be ensured. Based on these three elements as well as the trade-offs, BFT consensus, PoW consensus and other consensus algorithms thus came into being.
Without a universal distributed system, there will not be any universal consensus algorithms. The CAP theorem provides guidance and framework for the design of blockchain consensus and governance, determining the function and implementation of the distributed systems.
Despite the triangle being impossible, the protocol designers of cryptocurrencis strive to make things feasible.

Pingback: Layer 2 Solution for Bitcoin and Ethereum | EastShore Mining Devices